Facet Follies – May 2022
Did You Know?
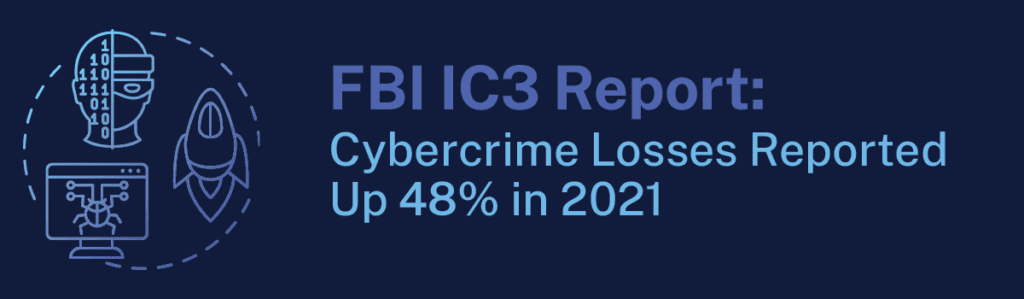
The dark web could now be considered the world’s third largest economy, with experts estimating that cybercrime brought in over $6 trillion in 2021, according to the FBI’s annual Internet Crime Report, which documents cybercrime trends. The Bureau recorded 847,376 complaints from businesses and consumers, and over $6.9 billion in losses from the U.S. alone, a 48% increase from 2020.
How did such an increase happen? For one thing, it’s gotten easier to hire out cybercrime. Previously the purview of criminals with coding and technical skills, the booming cybercrime-as-a-service market means that nearly anyone can buy the tools to ransom data, install malware, steal information, and conduct other illicit cybercrime activities, without any special skills.
As it becomes easier for cybercriminals and crime groups to take advantage of businesses and consumers worldwide, your business’s security strategy matters more than ever. Start with a security assessment from Facet to see where you stand and the actions you can take as a business leader to protect your company and your future.

It may sound simple, but pressing the Windows Key+L when you step away from your computer can save your business from serious security threats.
Although phishing emails and other “virtual” scams make up the bulk of cybercrime activity, some hackers will try to physically access a computer on a company’s network to steal data. This tip is especially important if you have computers in a public area.
On a Windows PC, pressing the Windows Key+L will lock your PC and take you to the sign-in page. On a Mac, Ctrl-Cmd-Q will do the trick and lock your device.
Like many things, virtually locking up your devices is part of building a vigilant security culture within your organization.
Does your organization need help making a game plan for cyber resilience? Facet offers free cybersecurity assessments for businesses! You will receive valuable information about your company’s current security and know where you can improve to prevent breaches and attacks.
Request more information below.

“Shadow IT” is the practice of using programs and websites for work activities without the knowledge or approval of the organization’s IT provider or IT department. While this is an “older” term, the practice has become increasingly common as file sharing sites grow in popularity and upload speeds quicken.
Software like Dropbox and Google Drive can help your team collaborate and work together easier, especially at a time when many companies are choosing a work-from-home or hybrid approach for their employees. However, it’s important to weigh your options and acknowledge the risks of using these tools.
If one of your employees quit without notice today, or had to be terminated unexpectedly, would you know where all their important work documents are stored? Would they be on their workstation, a cloud solution your IT team set up, or dispersed on the employee’s personal file storage accounts?
It’s important to ask these questions because a situation like this will almost certainly happen at some point to every business. If important files are on an employee’s personal storage, they can walk away with customer data and other valuable information.
Not only does this open you up to the threat of a disgruntled employee taking customer data or other documents to a competitor, it also means that if their personal cloud storage is hacked, your data is as good as gone.
If you work in a regulated industry like healthcare, insurance, or finance, you especially need to be on the lookout for shadow IT programs. Doing your due diligence and putting in proper security and IT practices can save you from costly data privacy lawsuits in the future should you be audited.
The first step is to make sure that your IT firm or IT department is monitoring downloads and new software installations on company equipment as part of routine security practices. If you aren’t sure if your current provider does this for you, ask them. From here, you can choose to block or allow certain sites and downloads at the firewall level.
Additionally, offer your employees a better way to work collaboratively with cloud sharing programs made specifically for businesses. These programs allow employees to store work files for themselves and share documents and information within the organization. Call Facet today and ask for more information on options for secure work on the cloud.
In honor of our one-year anniversary in our new location, we’re sharing our first ever Facet Follies from 2014! Enjoy!

This month’s recipe is from Facet’s Customer Advocate, Nick Baker!
Nick says these crepes are “debatably my favorite food ever.” His recipe for authentic French crepes can be customized with a wide variety of savory and sweet ingredients for a different flavor every time you make them.
This recipe is also available on the blog.
Ingredients
2 eggs
1/4 cup butter, melted
2 1/2 tbsp sugar
1/2 cup all-purpose flour
1/2 cup milk
1/8 cup water
1/2 tsp vanilla
dash of salt
You can experiment with using only egg whites, only yokes, and other combinations depending on your preference. Its also fun to experiment with the flour type depending on ingredients used.
Breakfast Crepe
My favorite ingredient is simply honey.
Butter
Whip cream and strawberries
Sometimes I will crack and egg onto the crepe and cook it on the crepe adding cheese and other ingredients available. Then, folding the crepe in to quarters, making it easy to eat with your hands.
Savory Crepe
Ham and Cheddar
Mozzarella and Pepperoni
Be creative
Now that we’ve made it through the holidays and into the coldest part of the winter, let’s brighten things up by discussing some easy resolutions you and your team can make this year to reach your cybersecurity goals!
To make a resolution stick, experts agree it should be structured around habits and behaviors, not lofty, pie-in-the-sky wishes or outcomes. If your goal is to be more financially responsible, for instance, they suggest resolving to create a weekly budget that you follow religiously.
Similarly, if you make a resolution for your business, structure it around habits and real, measurable outcomes. Don’t just resolve to get your IT in order, or get your data more secure. Success for these goals isn’t easily measured, so try for something a little more pinpointed.
I challenge you to choose one of the following resolutions for you and your team, and write them down.
Why write them down? Often, a resolution is just a wish until you write it down—then it becomes a goal.
Even if you only choose one of the following goals, these small changes can make a big difference in your company’s security.
Conduct weekly, monthly, or quarterly security training with your team. We have videos you can share with your team, or we can provide written resources that you can teach from.
Why do this?
If you’re still using the same password for multiple accounts, resolve to change them to a unique value as you visit each site.
Why do this?
Implement an MFA (multi-factor authentication) strategy.
Why do this?
Increasing security can feel like an overwhelming task to undertake, but you can make real progress one step at a time.
Facet Technologies specializes in managed services and IT in Peoria, IL, surrounding areas, and nationwide. We can find a security solution that works for you, offering firewalls and other hardware appliances, security software, dark web scanning, and more.
Fill out our contact form below to find out more about our Security Suite and set up an audit of your network security.

This month’s recipe is from a Facet team member known Jason Hahn, Facet’s Director of Business Solutions and #1 Cardinals fan. Jason has been a part of the Facet team for over 20 years now!
Jason is sharing his favorite salsa recipe. The ingredients are blended in a food processor to get a great smooth consistency! Let it chill for a couple hours to get the best flavor. Jason says that his wife and daughters love this salsa on taco night!
Chili’s Copycat Salsa
1 – (14 1/2 ounce) can tomatoes and green chilies
1 – (14 1/2 ounce) can whole canned tomatoes (plus the juice)
4 – teaspoons jalapenos (canned,diced, not pickled)
1⁄4 – cup yellow onion (diced)
1⁄2 – 3⁄4 – teaspoon garlic salt
1⁄2 – teaspoon cumin
1⁄4 – teaspoon sugar
1. In food processor place jalapenos and onions.
2. Process for just a few seconds.
3. Add both cans of tomatoes, salt, sugar, and cumin.
4. Process all ingredients until well blended but do not puree.
5. Place in covered container and chill.
6. A couple of hours of chilling will help blend and enrich the flavor.
7. Serve with your favorite thin corn tortilla chips.
Recipe courtesy of copykat.com