Facet Follies – June 2020

See all the Facet Follies in one place by clicking here!

See all the Facet Follies in one place by clicking here!

How far would you go to protect your company’s data? How about your customers’ data?
Every day, business owners are confronted with this exact question when they become victims of ransomware schemes. According to an industry report by Coveware, the average ransomware payout in the third quarter of 2020 was $233,817 (source). Some are much cheaper, even as low as $60,000, but cyber criminals are smart enough to tailor their ransom amount to the size of the company and how much they think you’ll be able to fork over quickly.
You may choose to negotiate the amount. This is expected—often the total payout can be negotiated down by as much as 20%, but after that point, you’re at the mercy of your captors. If you choose to pay the ransom, you may get your data back, but there is no guarantee (honor among thieves and all that). Studies show that about 60% of people who pay the ransom get all or most of their data back. Others get only a small amount, and some never see it again. Scary! Plus, companies that pay large ransoms encourage hackers to continue to pursue payouts with ransomware. They’re only in the business because it remains profitable for them.
That’s why I have backups, you may be thinking. It’s true; backups can save you from lost data and prevent downtime. Recently, however, the bad actors have upped the stakes for compromised companies: if you don’t pay, they’ll post your data and your clients’ data to dark web marketplaces for sale. As with getting your data back, there is no guarantee that paying the ransom will prevent this in 100% of cases. Some criminal syndicates that run ransomware schemes will immediately post a small amount of data on “bragging rights” websites, anyway. Trust me, you can’t win here.
The best method proven to prevent email-based ransomware attacks is a solid defense strategy. You can often intercept an email ransomware attack at a couple points in the process: you can prevent the email from reaching your inbox, or you can prevent the software from being downloaded.
Prevent ransomware emails from reaching your inbox with the help of an email filtering solution. Many emails with ransomware attached are designed to look like they came from an internal source. A good email filter can catch many of these emails before they ever hit your inbox, quarantining them to prevent ransomware and other malware.
Your email may have a “built-in” spam filter, but these filters are not the most accurate when it comes to keeping harmful emails in quarantine. Email filters like those offered by Facet use artificial intelligence (AI) and other tools to successfully identify and block ransomware attempts, even when they come from legitimate-looking sources. These filters go several steps further to prevent access to your system than traditional spam filtering included with email.
I know you’ve been hearing a lot about employee education from us lately. It’s because it’s the single most effective way to prevent a ransomware attack on your system. Email filters work wonders, but no method prevents 100% of attacks. Your team must practice vigilance and awareness to properly avoid ransomware and loss of data.
Facet offers employee education in a few forms. In addition to resources for training that you can conduct yourself, we also offer phishing simulation services. Phishing simulations are a proven way to decrease your cybersecurity risk across your entire company.
Phishing simulations involve sending emails that mimic the characteristics of common phishing and ransomware emails. Instead of containing harmful software or truly stealing your credentials, however, the emails direct those who click on the “harmful” link or enter their password into the fake website to training videos and materials to better prepare them to identify future threats.
If you are already a Facet customer, consider a quick check-in to confirm that your security options and services are all up-to-date. Facet has recently hired a dedicated Security Analyst to assess current threats and industry trends, as well as a Customer Advocate to continue in our goal of better serving our customers. You can use the contact form below or call our main phone number to schedule an appointment and review your security options and recommendations.
If you are looking for an even deeper dive, consider a Security Plus Audit. The Security Plus Audit is an intensive evaluation of your company’s cybersecurity stance, including dark web dives and more. This service is an invaluable way to gain insight into your position and get a roadmap to cybersecurity peace of mind.


Join us for Business After Hours with the Peoria Chamber of Commerce at Facet’s new headquarters!
Thursday, June 10th
4:30PM – 6:30PM
3024 W. Lake Ave.
Peoria, IL 61615
We will have raffle prizes including a Cards jersey, Tervis tumblers, and gift cards!
Food, soda, beer and wine will be provided. We will have an outdoor tent and cocktail area as well as tours offered through the new building.
Register ahead of the event on the Peoria Chamber of Commerce website here.
We can’t wait to see you! Feel free to reach out with any questions.

This month’s recipe is courtesy of Network Technician Brad Strickler. He says this recipe is a favorite that is asked for often at family gatherings.
Snickerdoodle Cheesecake
Ingredients:
1 log sugar cookie dough
3 Tablespoons cinnamon sugar
3 9-oz. blocks cream cheese (softened)
1 cup granulated sugar
1/4 cup sour cream
3 large eggs
2 teaspoons vanilla extract
1/4 teaspoon ground cinnamon
pinch of salt
Directions:
1. Preheat oven to 350 degrees and grease an 8″ springform pan.
2. In a large bowl, combine cookie dough annd cinnamon sugar, mix until evenly incorporated. Press half of the dough into the bottom of the springform pan (Leftover dough can be baked as cookies).
3. In another large bowl, beat cream cheese until smooth. Add sugar and sour cream and beat until light and fluffy. Add the eggs one at a time, beating well between each addition. Stir in vanilla, cinnamon and salt. Pour batter over the cookie dough crust.
4. Bake until slightly jiggly in the center, about 1 hour. Turn off the oven and open the door slightly and let the cheesecake cool for 1 hour. Then refrigerate until completely cooled, from 4 hours to overnight.
5. Roll remaining dough into small balls then flatten slightly on a baking sheet. Bake until starting to turn golden around the edges, about 10 minutes. Let cool on a cooling rack.
6. Before serving, sprinkle top of cheesecake with extra cinnamon sugar. Garnish with snickerdoodle cookies (or snack on the cookies separately).

IT security experts will often tell you that employees are the greatest security vulnerability in any company. We warn of social engineering emails and phone calls, reused passwords, work emails used on personal accounts, and dozens of other behaviors that can put your business at risk for breaches and hacks.
According to a cybersecurity report by Kaspersky in 2019, 90% of data breaches occur due to human error. Other sources cite “employee negligence” as a top cause of data breach. Negligence is its own issue, but it’s important to take responsibility as an employer for proper training that could prevent a data breach.
Employee education can save your company millions of dollars. Consider employee education and training the cheapest form of IT security available to companies of any size. Be sure to also take into account the potential costs of data loss—how much would you lose in time and resources in the event of a breach?
Instead of thinking of employees as a liability, consider your team to be a great untapped asset for network security. These five easy behaviors can make a huge difference in your security!
1. Lock your computer when you step away:
We may trust our coworkers with our PC, but there are security risks involved when you leave your computer unattended and open. When you walk away from your computer, take a second to press Windows Key + L to lock your screen and protect any sensitive data.
2. Avoid flash drives, especially “found” flash drives:
Flash drives are useful, but they can easily be loaded with malicious programs or used to steal data. One of the oldest forms of social engineering involves dropping a flash drive in a parking lot and waiting for an employee to pick it up, thinking it simply a lost flash drive, and put it in a computer to see who it belongs to (or to snoop around). It can then install software on the employee’s computer, sometimes without the employee ever knowing. If it’s not your personal flash drive, avoid putting it in your computer.
3. Don’t let just anyone into your server area:
Be careful who you allow to get access to your server. Sometimes people will pose as IT providers to get physical access to your server. If you did not have a scheduled appointment and don’t recognize someone who says they’re from Facet, you can always call us to see if we sent someone out to your location.
4. Verify email senders before clicking links:
Always check the “from” field in any email you get before clicking on a link. Many scams involve fake links (and “from” addresses that are spoofed) to get your login information. If you get a password reset email or other account notice unexpectedly, go directly to the site in question via a browser rather than clicking the link in the email. These couple seconds can save you a lot of trouble!
5. Develop a healthy sense of skepticism:
The most important thing to teach your team is to treat most online and phone interactions with a healthy sense of skepticism. This means taking that extra few seconds to really think about something before pulling the trigger, and not letting a sense of urgency take over. For example, if you get an email with an offer, take a little extra time to verify that it’s a legitimate offer from a real, reputable company.
Employee training may take time, but the practice can save your business thousands in the long-term. For more information, or to request on-site employee training, contact Facet today. We offer a variety of training, including phishing email simulations, training videos, and printed materials.
This month’s recipe is from Facet’s Accounting Clerk, Tammy McBride! Tammy says this recipe is a favorite at parties and gatherings and is great if you love Snickers bars and apples.
Ingredients:
Instructions:

How long will a computer last? When do I need to replace my computer?
We get these questions often here at Facet, but it’s not easy to formulate an answer in most cases. There are no fixed rules here, as it often comes down to personal preference.
We can, however, offer some guidance on how to keep your current PC in good working condition. What can you do to extend the life of your computer? There are a few tricks that can help you extend the life of your PC, but it’s also important to understand that even under perfect circumstances, all computers will eventually need to be replaced.
All hardware fails, and we can’t accurately predict the lifespan of any one component. Keep this in mind both when purchasing and planning for the retirement of a computer.
Hardware components fail on a bell curve. That is to say, when any one component is mass manufactured, some individual pieces will fail early on. Sometimes this will fall within the manufacturer’s warranty, but bear in mind that warranties are typically designed to end before any considerable number of failures occur (this is why “Black Friday special” PCs often have 3-month warranties attached—we see a lot of these PCs in March and April). Most will fail somewhere in the middle, and a few will outlast the rest and fail much later. There’s no great way to tell where, say, your laptop’s track pad or LCD falls on that bell curve. There are too many individual components in any given PC to control every variable.
Some environmental factors do speed up the decay and subsequent failure of hardware components in your PC. A few such factors include:
For computer repair in Peoria, IL, call Facet Technologies at (309) 689-3900. We offer full-service computer repair, virus removal, diagnostics, hardware upgrades, and more. We also offer custom-built desktop computers and Lenovo laptops to fit your needs.

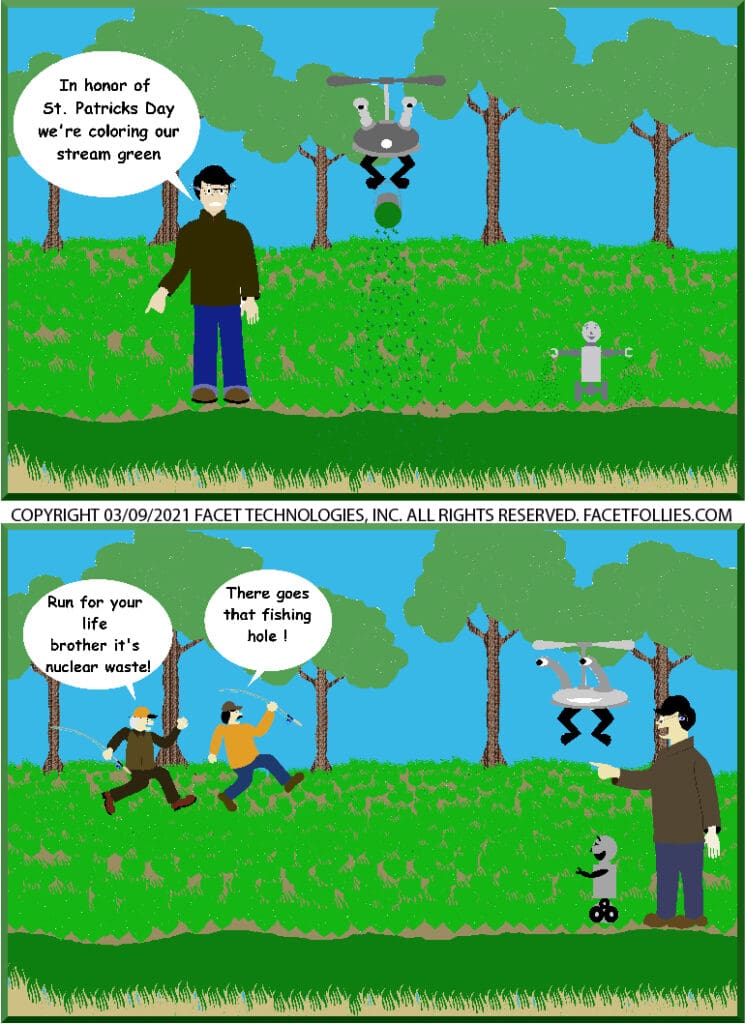
Facet Follies is a monthly tech cartoon by Mike Wright.
Want more Follies in your inbox? Sign up for our newsletter below.